introduction: for site group deployments that hope to improve search performance and ensure security and compliance in the korean market, this article provides executable deployment directions and precautions from the perspectives of server selection, network design, security control, and seo optimization to help the operation and maintenance and seo teams advance collaboratively.
why choose south korea kt station group server
choosing local hosts such as south korea's kt can improve the local access speed and the geographical relevance of search engines, which will help improve the indexing efficiency and experience of korean or korean users. at the same time, local operators usually provide more stable international links and local regulatory support, which helps long-term seo performance.
geography, bandwidth and seo impact
servers are located in south korea's preferred capital or major computer rooms, which can significantly reduce latency and increase page loading speeds. bandwidth and uplink stability directly affect the crawling frequency and page response time. you should choose a solution with sufficient peak capacity and scalable bandwidth to support concurrent crawling and access.
deployment principles with equal emphasis on security
while the station group is pursuing traffic and coverage, it must put security in an equally important position. it is recommended to start with the three-layer protection of the network layer, host layer and application layer, and formulate the principle of least privilege, isolation strategy and audit mechanism to reduce the chain risk caused by a single point of breach.
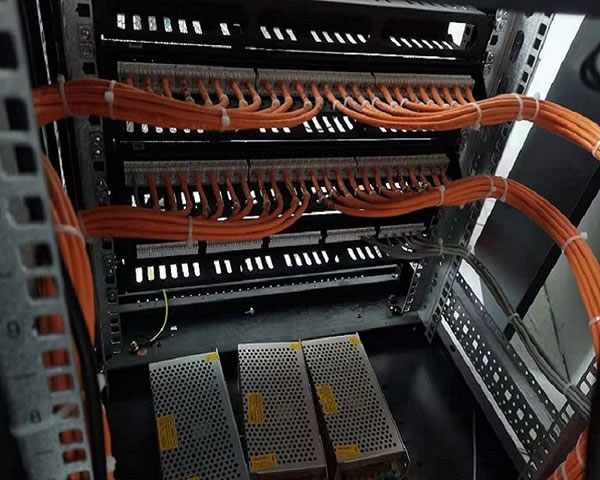
access control and network isolation
isolation between station groups is achieved through vlan, private subnets and security groups, and the management panel and sensitive services are placed on a dedicated network segment for management. use ip whitelist, vpn or springboard to restrict management access, enhance the security of operation and maintenance channels, and avoid backend leakage affecting all sites.
data encryption and backup strategy
the transport layer uses tls, and data at rest is encrypted on disk or object storage. develop a hierarchical backup strategy: regular full backups, frequent incremental backups, and off-site backups to ensure rapid recovery in the event of a single point of failure or data damage, while meeting compliance and business recovery requirements.
seo friendly server configuration
server configuration needs to take into account crawling efficiency and page performance: enable http/2 or http/3, properly handle gzip/compression, and set the correct content-type and cache-control headers. ensure stable site response and correct 302/301 jumps, and reduce search engine indexing errors.
site group domain name and site distribution strategy
site group domain name strategies should avoid duplicate content penalties: ensure clear site themes and independent content when using geographical subdomains or subdirectories. proper use of robots.txt, sitemap and hreflang (if multi-lingual) is used to help search engines correctly crawl and identify the site weight distribution.
server response and cache optimization
reduce the pressure on the origin site and improve the time to first byte (ttfb) through edge caching (cdn), reverse proxy and local caching strategies. carry out reasonable caching stratification for dynamic pages, set short, medium and long-term caching strategies and refresh important pages regularly to take into account seo freshness and performance.
compliance, logging and monitoring maintenance
comply with korean data protection and security regulations and design minimum collection and retention procedures for user data. configure centralized log collection, backup, and long-term storage strategies to ensure audit traceability, and clarify log retention periods and access permissions.
abnormal monitoring and alarm process
establish a monitoring system covering links, hosts, applications and security events, and set thresholds and automated alarms. combined with siem or centralized event management, the response process and responsible persons are clearly defined to ensure that traffic abnormalities or security incidents can be quickly located and dealt with when they occur.
deployment process recommendations (brief steps)
it is recommended to follow: demand assessment → site selection and bandwidth planning → network and isolation design → host and storage configuration → security baseline and access control → seo performance tuning → backup and monitoring online → grayscale release and verification. each step is coordinated with documentation and rollback plans to ensure repeatability and auditability.
summary and suggestions
when renting and deploying servers in the korean kt station cluster, seo and security should be planned simultaneously: prioritize the appropriate geographical location and bandwidth, implement network isolation and minimum permissions, deploy encryption and backup, and do seo configuration and performance optimization before and after deployment. continuous monitoring and compliance auditing are key to ensuring long-term stability and search performance.

- Latest articles
- Small And Medium-sized Enterprises Deploy Cambodian Cn2 Network To Save Costs And Improve Quality
- Case Study: Cn2 Malaysia’s Quantitative Improvement And Benefit Assessment For User Experience
- Comparative Test On Packet Loss Between Hong Kong Return Cn2 And Ordinary Return Lines
- Detailed Explanation Of The Difference Between Taiwan Server Abbreviation Cloud Host And Vps And Recommended Application Scenarios
- Night Duck Korean Native Ip Service Introduction And In-depth Analysis Of Suitable User Scenarios
- Evaluation Of The Impact On Seo And Access Speed Of This Website Server Being Set Up In The United States
- Enterprise Procurement Vietnam Vps Official Website Entrance Backend Management And Invoice Issuance Process Description
- Vietnam Native Ip Vps Purchasing Guide Teaches You To Identify Real Ip And Shared Resources
- Best Practices For Selecting Malaysian Vps Unlimited Traffic Packages Based On Actual Needs
- Analysis Of The Key Location Factors Affecting Operational Security Where The German Railways Signal Equipment Room Is Located
- Popular tags
-
Analysis Of The Group Image Of Korean Boy Groups In Red Carpet Review
this article analyzes the group image of korean boy groups in red carpet events, including clothing style, stage performance and public impression. -
Introduction To Common Communication Tools And Activity Collaboration Processes After Joining The Korean Support Site Group
introduces common communication tools, collaboration processes and emergency response suggestions after joining the korean support station group, helping new members quickly integrate and effectively participate in fan support activities. -
Explore The Application Of Korean Native Ip In Cross-border E-commerce
explore the application of korean native ip in cross-border e-commerce and analyze its market potential and development strategies.